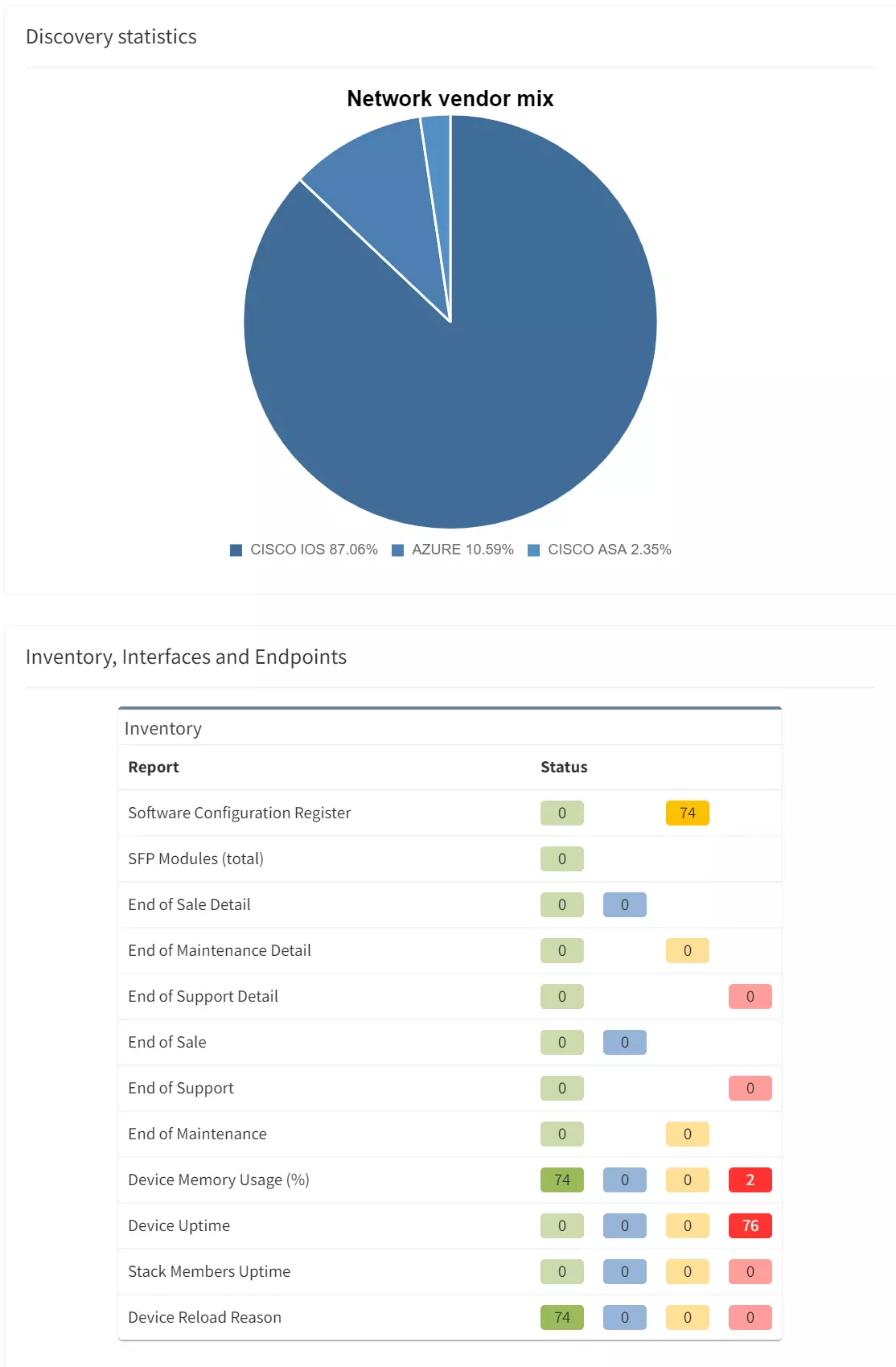
During the past year of the platform development, we added more API vendors than vendors we discover over SSH. That's a big milestone! There are currently eight different API vendors, that you can add to your traditional high-performance hardware infrastructure in IP Fabric. And it clearly sets the stage for the near future.
The next main feature that's undergoing extensive development is the path simulation. With an excellent CCIE/CCDE level knowledge pool and outstanding software engineers in the team a simple path testing tool in IPF version 3, turned into a deep-level simulation engine for very complex end-to-end scenarios. In the latest release you can:
The release of Version 4.3 is the biggest one yet when it comes to the number of new features and updates. So please sit comfortably and enjoy this written virtual tour. We will mention newly added technologies for F5, Extreme, and HP Aruba CX, the new system features like Single-Sign-On (SSO), or a new attribute model for integration purposes.
It's been more than twenty years since Amazon introduced its web-based retail services. The cloud computing infrastructure Model gave them the flexibility to use their computer’s capacity much more efficiently. Soon after, other large organizations followed their example.
Just about ten years ago, a lot of organizations had reserved opinions about public cloud security and chose private or hybrid cloud models instead. With moving resources to the cloud, supporting network infrastructure has to follow. It started with translating standard hardware-based operating systems on virtual resources (we have high-performance SRX4100 in our data center, then we should deploy vSRX in the cloud to solve the security in the cloud). But soon after engineers realized that transferring the concept doesn't necessarily mean keeping the boundaries of the previous hardware parent.
The main advantage of the cloud is resource flexibility and speed of deployment. Anytime we put boundaries around that we lose the main concept value.
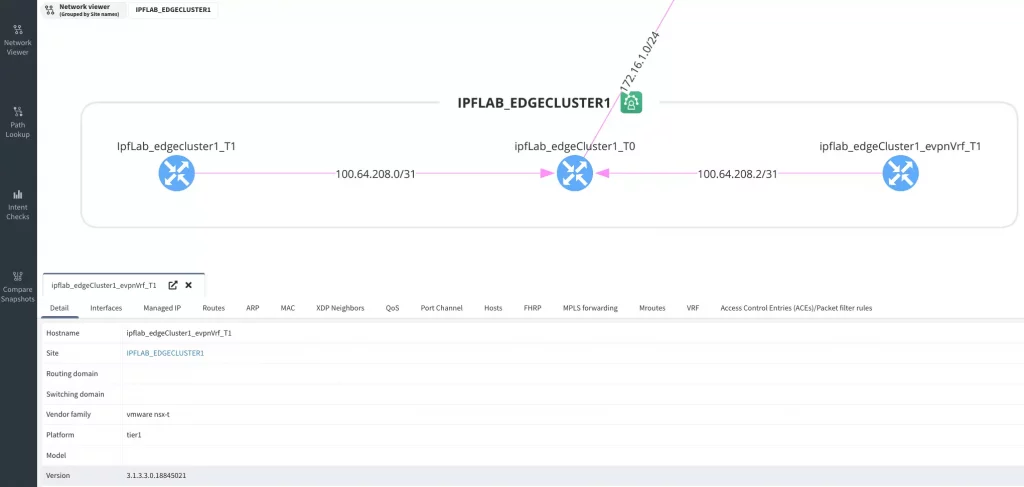
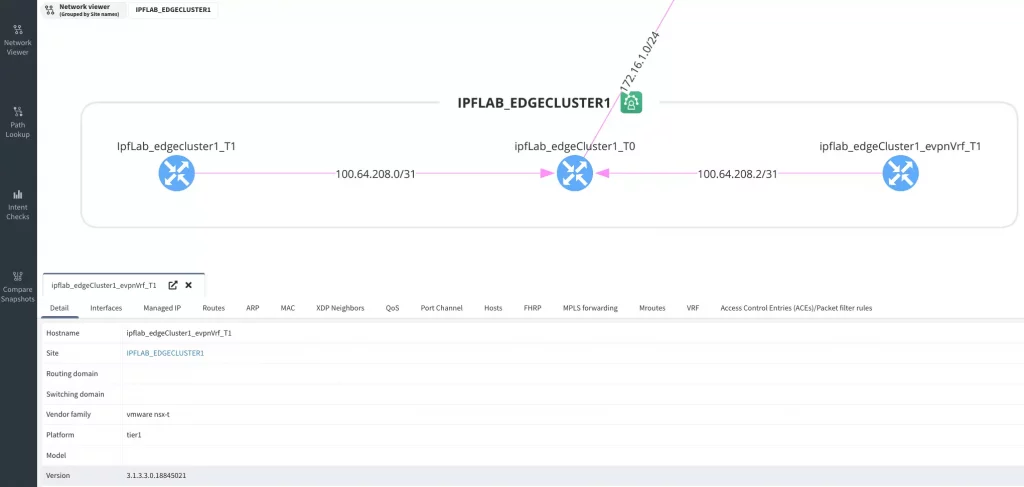
Adding a new NSX-T network into IP Fabric is simply adding a new API vendor in Settings. Users will get visibility into L2, L3 interfaces, ARP records, routing, and much more including path simulation capabilities.
Initial VMware NSX-T includes basic discovery and data collection for network mapping, establishing forwarding edges, and allowing path lookup.
With the latest 4.3, we cover only the IaaS (Infrastructure as a Service) part of the cloud. Azure Cloud Compute provides an abstract view of the Azure physical infrastructure.
Following Azure Cloud elements are supported:
and elements related to a Virtual WAN solution (Azure Virtual WAN Overview):
The path towards full SD-WAN support is on its way and the SilverPeak is another down the list. Silver Peak Unity is the premier software-defined WAN (SD-WAN) architecture for today’s enterprise. Unity is a virtual WAN overlay that enables customers to deploy hybrid or all-broadband WANs using multiple types of connectivity, including MPLS, cable, DSL, LTE, etc.
To add SilverPeak SD-WAN devices into IP Fabric, we need to add API for the Unity Orchestrator.
Another added vendor is Brocade ICX, which doesn't need an introduction.
IP Fabric as a platform that is used across teams has always been the plan. Support for a single sign-on (SSO) will make the platform more accessible with less configuration and management effort. Local or LDAP users are available already, but SSO is becoming a standard.
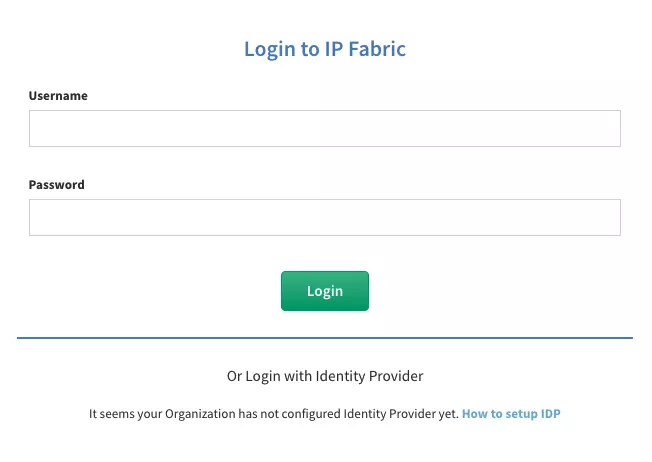
To set up your identity provider (IDP) properly, please, contact our Support or System Engineering team. The DEX standard is used to support SSO in IP Fabric.
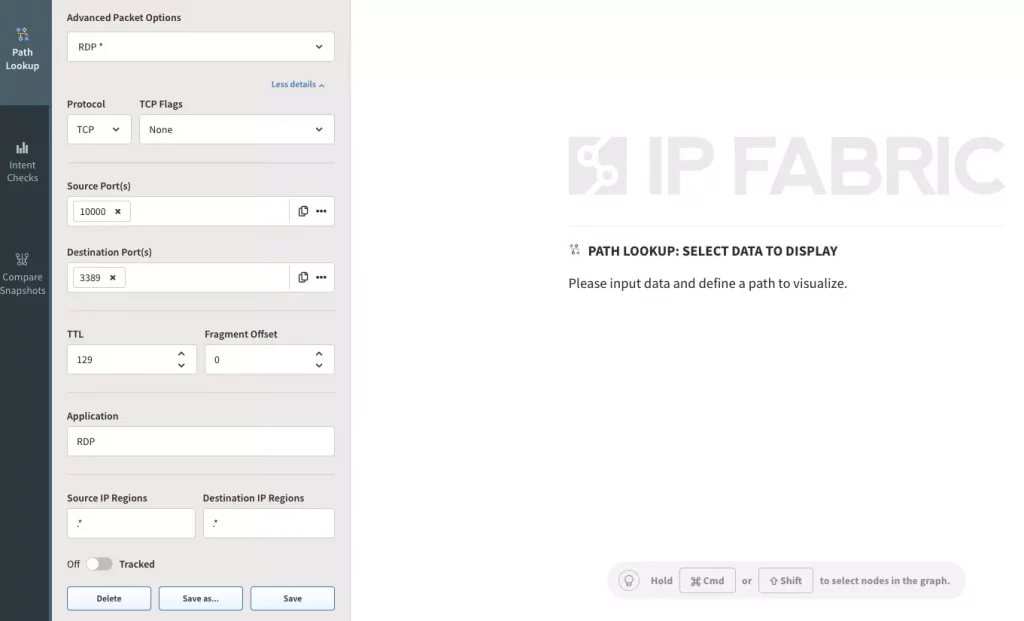
I am thrilled to announce another path simulation update. With a focus on new use cases based on the feedback we have received over time, there's a new batch of upgrades to our previous path. The new user interface is very similar to one we have in version 4.2 and earlier, but a little different.
Behind this new option are endless possibilities. For many, this new feature can remain unnoticed, but it's opening a lot! The automatic option works as expected, it's a standard path simulation from source to destination. On the other hand, the user-defined algorithm is a game-changer. It allows setting an edge or multiple edge router or edge firewalls as a source for the path.
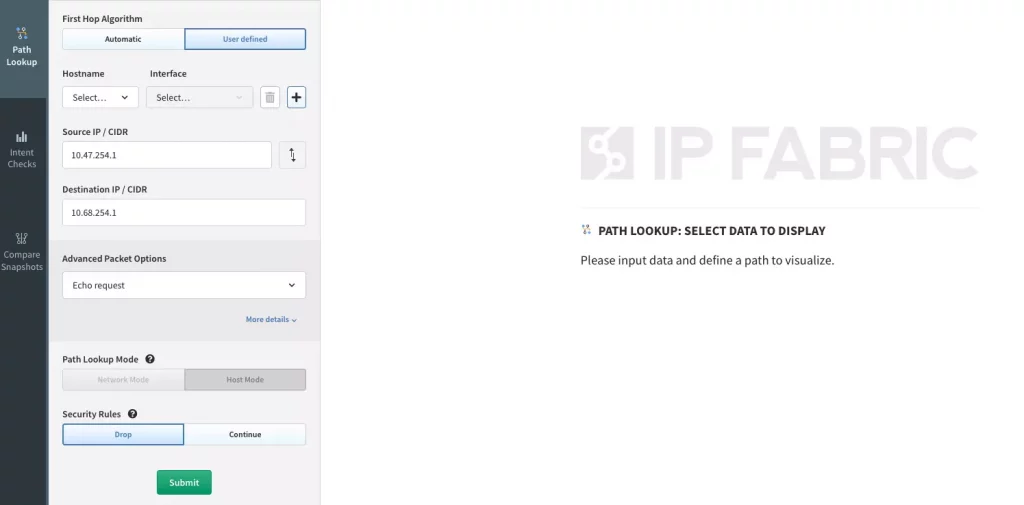
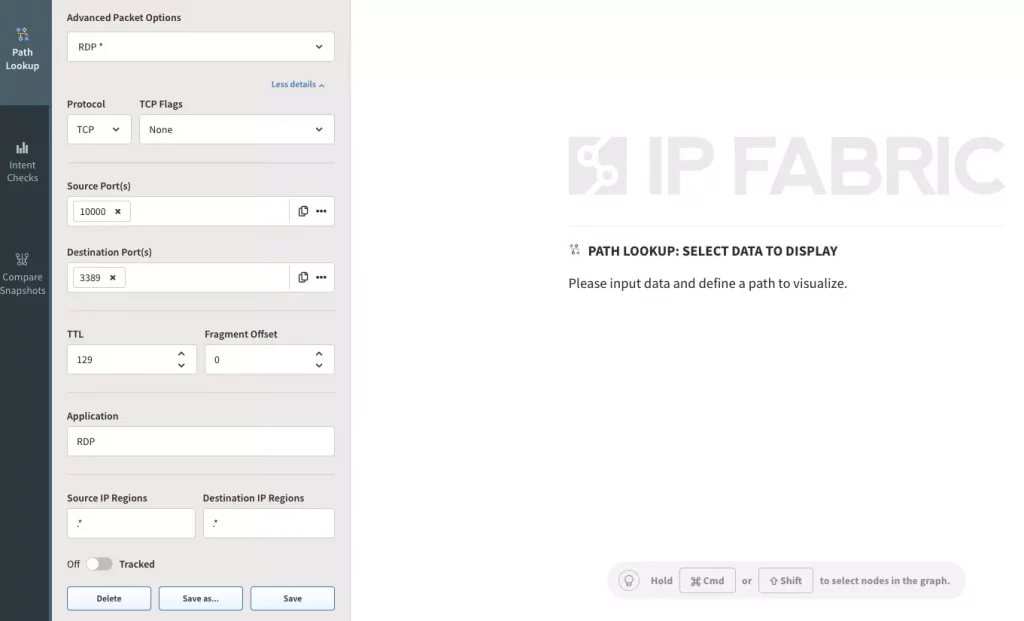
The path simulation remains with standard options unless we open advanced options with the 'More details' button. IP Fabric's Network Automation and Core Development team joined forces and created an ultimate testing platform for your security! For many users, it may stay unnoticed but will be operated extensively for advanced users and integrations over API. Here's what's new:
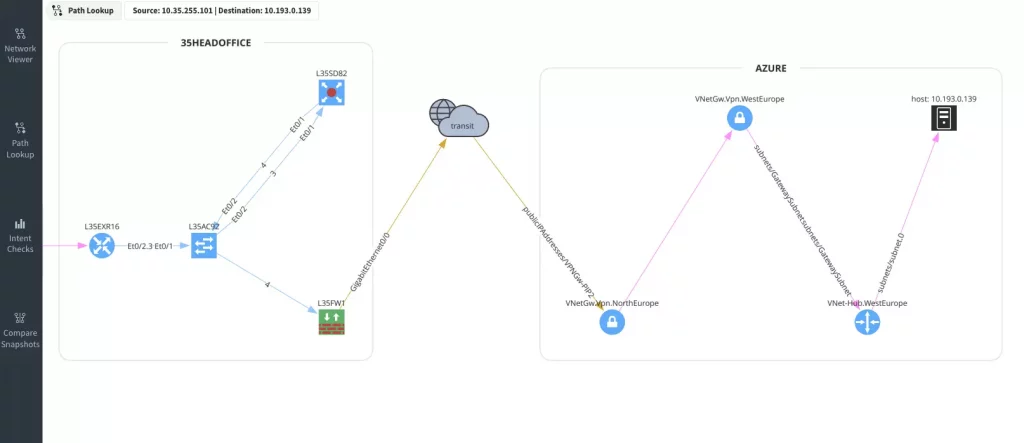
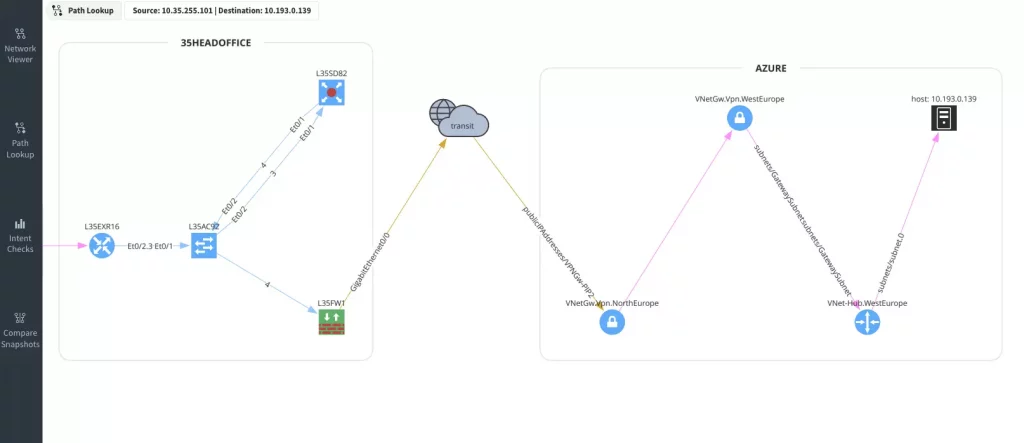
A logical next step for what's been missing since we implemented cloud and SD-WAN vendors is to add simulation capabilities. Simulation is now operational for AWS, Azure, NSX, and Cisco Viptela. Simulation is yet not available for Versa SD-WAN - we are currently facing difficulties of getting all required data over API and will probably need to implement hybrid (API + SSH) discovery.
This new feature may seem small and unimportant, but none of that is true. Our backend developers worked hard to start the transformation to an attribute-based platform, now why is that important?
There's one attribute that is available in IP Fabric already, it's the Site. The site is defined with the Site Separation rules (RegEx or Manual) and its primary function is to group devices together based on certain logic. That has worked well so far, but the challenge comes when we decide to integrate IP Fabric's data with another source of truth. Then we are to translate IP Fabric's logic to a different source-of-truth logic to create interoperability.
A lot of customers have the grouping logic created already in another tool and to speed up IP Fabric deployment and make it easier to apply the logic that's been already in place, customers can use their attributes in IP Fabric.
Starting 4.3, it's possible to assign sites based on serial numbers over API and ultimately integrate known attributes from any inventory asset management system (Netbox, ServiceNow) into IP Fabric automatically. Please, contact the System Engineering team to discuss the current options. New features around the attribute model are coming soon, so stay tuned to this channel!
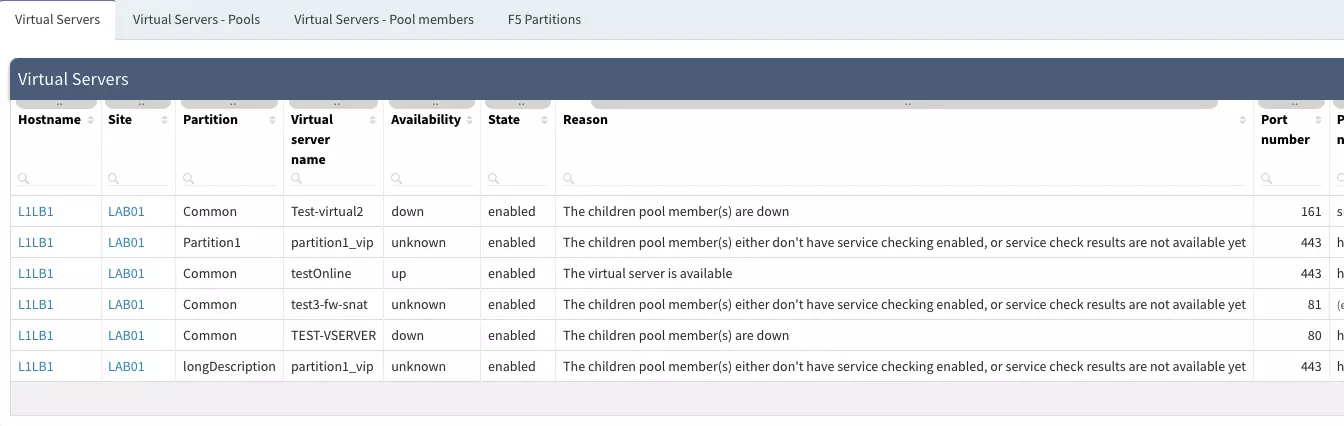
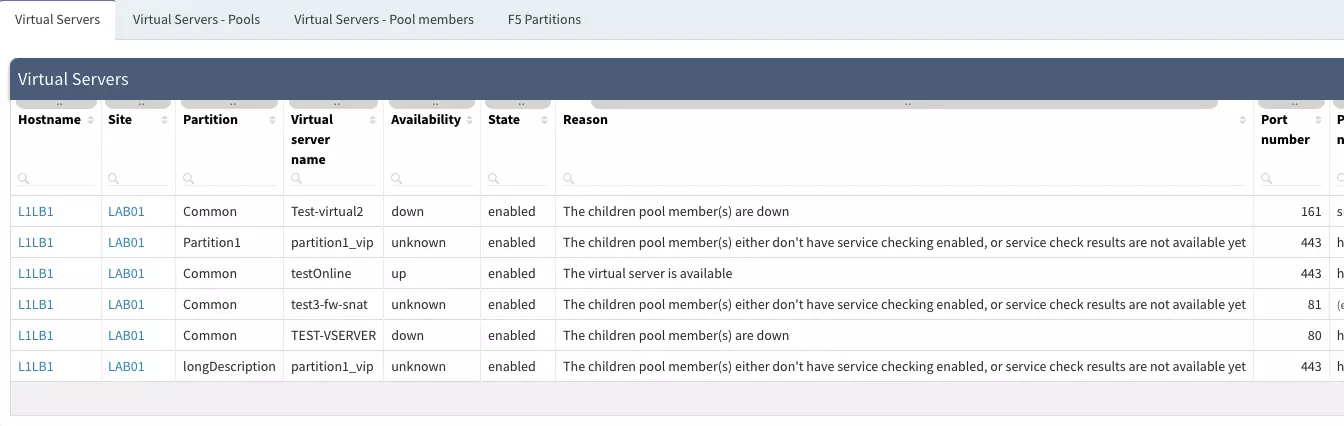
Big-IP/F5 has been supported for a while. IP Fabric's reading all network-related information (interfaces, VRFs, routing table, ...). The platform still relies on command-line interface (CLI) discovery and newly is reading Virtual servers, Pools, and Nodes to inventorize load balancing components for users. The following screenshot displays some of the information provided in Technology > Load Balancing.
There has been ongoing discussion after the major security rules GUI update in version 4.0. In version 4.0, we kicked off the security policies and access-list results in a tree-like layout to create a more human-readable format as visible on the screenshot below.
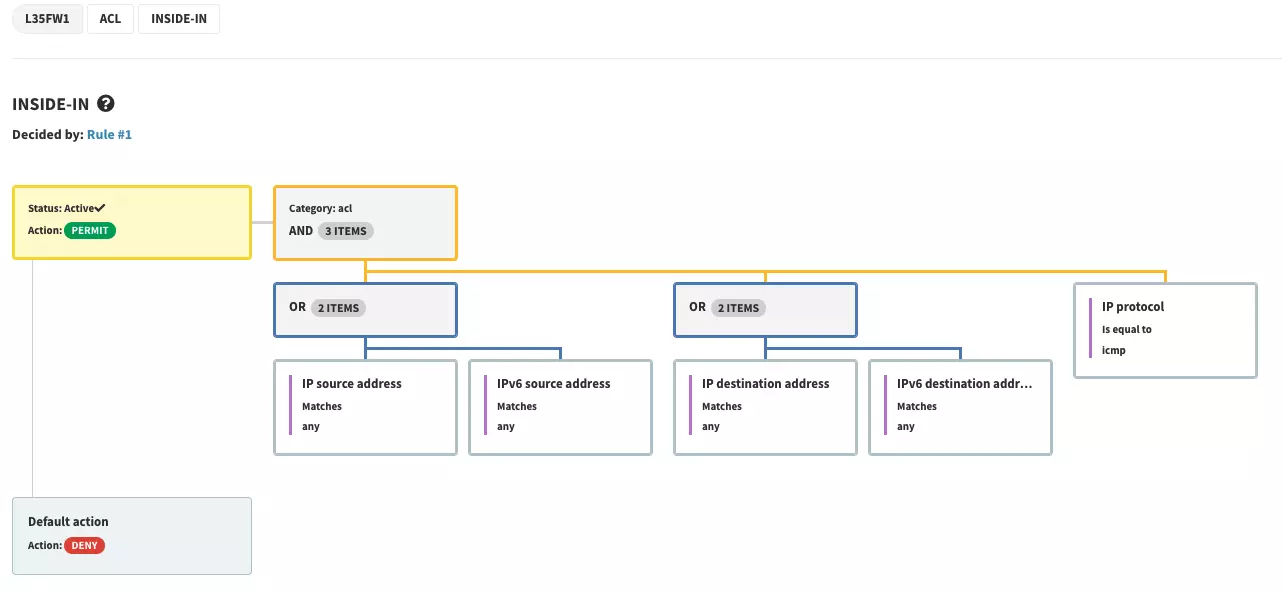
The human-readable format has its downsides and there couldn't be any intent rules created on top of the ACL or security policy rules. The overall security rules management was not easily exportable in the GUI and we were missing the search. Our 4.3 update is about to resolve that.
If you have found this article helpful, please follow our company’s LinkedIn or Blog, where more content will be emerging. If you would like to test our solution to see for yourself how IP Fabric can help you manage your network more effectively, please schedule a demo with our team: Request a Demo.
During the past year of the platform development, we added more API vendors than vendors we discover over SSH. That's a big milestone! There are currently eight different API vendors, that you can add to your traditional high-performance hardware infrastructure in IP Fabric. And it clearly sets the stage for the near future.
The next main feature that's undergoing extensive development is the path simulation. With an excellent CCIE/CCDE level knowledge pool and outstanding software engineers in the team a simple path testing tool in IPF version 3, turned into a deep-level simulation engine for very complex end-to-end scenarios. In the latest release you can:
The release of Version 4.3 is the biggest one yet when it comes to the number of new features and updates. So please sit comfortably and enjoy this written virtual tour. We will mention newly added technologies for F5, Extreme, and HP Aruba CX, the new system features like Single-Sign-On (SSO), or a new attribute model for integration purposes.
It's been more than twenty years since Amazon introduced its web-based retail services. The cloud computing infrastructure Model gave them the flexibility to use their computer’s capacity much more efficiently. Soon after, other large organizations followed their example.
Just about ten years ago, a lot of organizations had reserved opinions about public cloud security and chose private or hybrid cloud models instead. With moving resources to the cloud, supporting network infrastructure has to follow. It started with translating standard hardware-based operating systems on virtual resources (we have high-performance SRX4100 in our data center, then we should deploy vSRX in the cloud to solve the security in the cloud). But soon after engineers realized that transferring the concept doesn't necessarily mean keeping the boundaries of the previous hardware parent.
The main advantage of the cloud is resource flexibility and speed of deployment. Anytime we put boundaries around that we lose the main concept value.
Adding a new NSX-T network into IP Fabric is simply adding a new API vendor in Settings. Users will get visibility into L2, L3 interfaces, ARP records, routing, and much more including path simulation capabilities.
Initial VMware NSX-T includes basic discovery and data collection for network mapping, establishing forwarding edges, and allowing path lookup.
With the latest 4.3, we cover only the IaaS (Infrastructure as a Service) part of the cloud. Azure Cloud Compute provides an abstract view of the Azure physical infrastructure.
Following Azure Cloud elements are supported:
and elements related to a Virtual WAN solution (Azure Virtual WAN Overview):
The path towards full SD-WAN support is on its way and the SilverPeak is another down the list. Silver Peak Unity is the premier software-defined WAN (SD-WAN) architecture for today’s enterprise. Unity is a virtual WAN overlay that enables customers to deploy hybrid or all-broadband WANs using multiple types of connectivity, including MPLS, cable, DSL, LTE, etc.
To add SilverPeak SD-WAN devices into IP Fabric, we need to add API for the Unity Orchestrator.
Another added vendor is Brocade ICX, which doesn't need an introduction.
IP Fabric as a platform that is used across teams has always been the plan. Support for a single sign-on (SSO) will make the platform more accessible with less configuration and management effort. Local or LDAP users are available already, but SSO is becoming a standard.
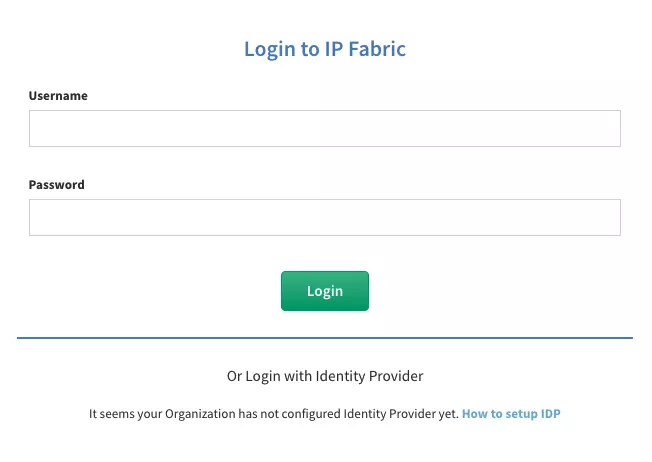
To set up your identity provider (IDP) properly, please, contact our Support or System Engineering team. The DEX standard is used to support SSO in IP Fabric.
I am thrilled to announce another path simulation update. With a focus on new use cases based on the feedback we have received over time, there's a new batch of upgrades to our previous path. The new user interface is very similar to one we have in version 4.2 and earlier, but a little different.
Behind this new option are endless possibilities. For many, this new feature can remain unnoticed, but it's opening a lot! The automatic option works as expected, it's a standard path simulation from source to destination. On the other hand, the user-defined algorithm is a game-changer. It allows setting an edge or multiple edge router or edge firewalls as a source for the path.
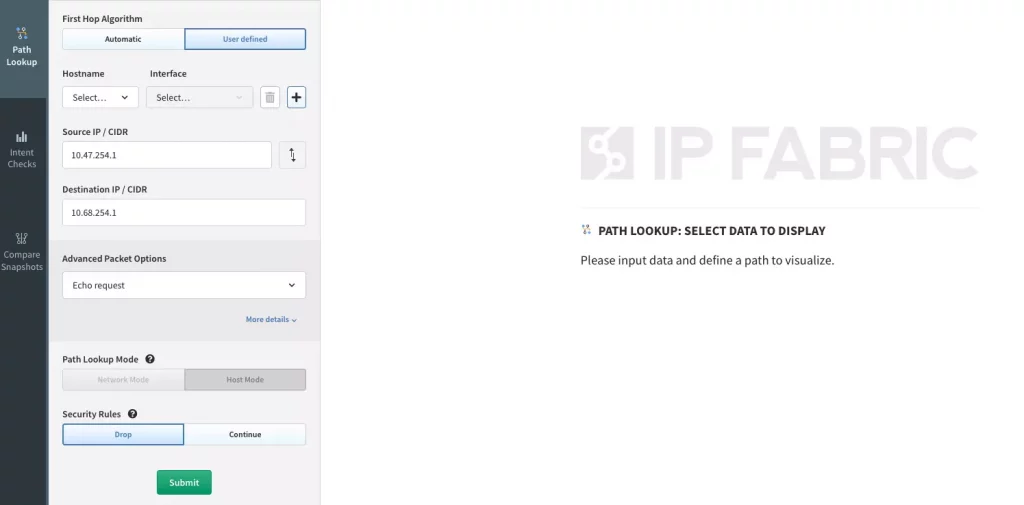
The path simulation remains with standard options unless we open advanced options with the 'More details' button. IP Fabric's Network Automation and Core Development team joined forces and created an ultimate testing platform for your security! For many users, it may stay unnoticed but will be operated extensively for advanced users and integrations over API. Here's what's new:
A logical next step for what's been missing since we implemented cloud and SD-WAN vendors is to add simulation capabilities. Simulation is now operational for AWS, Azure, NSX, and Cisco Viptela. Simulation is yet not available for Versa SD-WAN - we are currently facing difficulties of getting all required data over API and will probably need to implement hybrid (API + SSH) discovery.
This new feature may seem small and unimportant, but none of that is true. Our backend developers worked hard to start the transformation to an attribute-based platform, now why is that important?
There's one attribute that is available in IP Fabric already, it's the Site. The site is defined with the Site Separation rules (RegEx or Manual) and its primary function is to group devices together based on certain logic. That has worked well so far, but the challenge comes when we decide to integrate IP Fabric's data with another source of truth. Then we are to translate IP Fabric's logic to a different source-of-truth logic to create interoperability.
A lot of customers have the grouping logic created already in another tool and to speed up IP Fabric deployment and make it easier to apply the logic that's been already in place, customers can use their attributes in IP Fabric.
Starting 4.3, it's possible to assign sites based on serial numbers over API and ultimately integrate known attributes from any inventory asset management system (Netbox, ServiceNow) into IP Fabric automatically. Please, contact the System Engineering team to discuss the current options. New features around the attribute model are coming soon, so stay tuned to this channel!
Big-IP/F5 has been supported for a while. IP Fabric's reading all network-related information (interfaces, VRFs, routing table, ...). The platform still relies on command-line interface (CLI) discovery and newly is reading Virtual servers, Pools, and Nodes to inventorize load balancing components for users. The following screenshot displays some of the information provided in Technology > Load Balancing.
There has been ongoing discussion after the major security rules GUI update in version 4.0. In version 4.0, we kicked off the security policies and access-list results in a tree-like layout to create a more human-readable format as visible on the screenshot below.
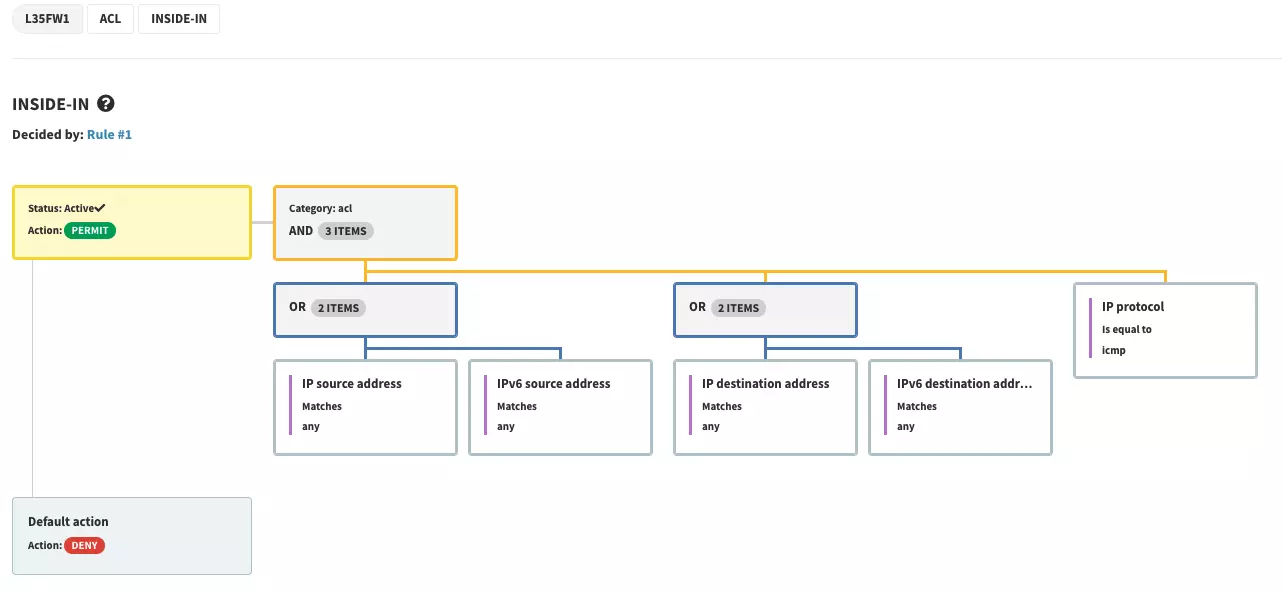
The human-readable format has its downsides and there couldn't be any intent rules created on top of the ACL or security policy rules. The overall security rules management was not easily exportable in the GUI and we were missing the search. Our 4.3 update is about to resolve that.
If you have found this article helpful, please follow our company’s LinkedIn or Blog, where more content will be emerging. If you would like to test our solution to see for yourself how IP Fabric can help you manage your network more effectively, please schedule a demo with our team: Request a Demo.