Since the mid-2000s, quite a few network security policy management (NSPM) platforms have arrived on the market. Whilst they are effective at what they do, just how useful are they in isolation? It depends on who you ask. Network security teams would probably agree that NSPM solutions are great, whereas infrastructure teams would likely disagree. But why? What do NSPMs do exactly? And more importantly, is there a way to improve them? We think so. We believe the answer lies in Network Assurance.
NSPM platforms can do quite a bit to improve overall network security:
Based on this list alone, it should be simple enough to put an NSPM solution in place and call it a day, right? After all, my security rules are being checked, and I know what impact data flow is having on my connectivity. Well think again.

While NSPM platforms provide SOME visibility, teams don't necessarily get the full picture that they need. This is because NSPM platforms typically only begin at OSI layer 3, the routing layer. When trying to discover and document your network, NSPMs only provide a restricted view of the entire picture.
Modern networks are inherently fragmented. Combine traditional network elements like routers and switches with a mixture of private and public cloud environments, and suddenly, ensuring comprehensive security policy implementation across all environments becomes more taxing.
Network assurance rounds out this view. As assurance views modern network infrastructures as a 'network-of-networks', it is geared toward understanding how network environments interconnect and interact, and how a change in one area can impact others.
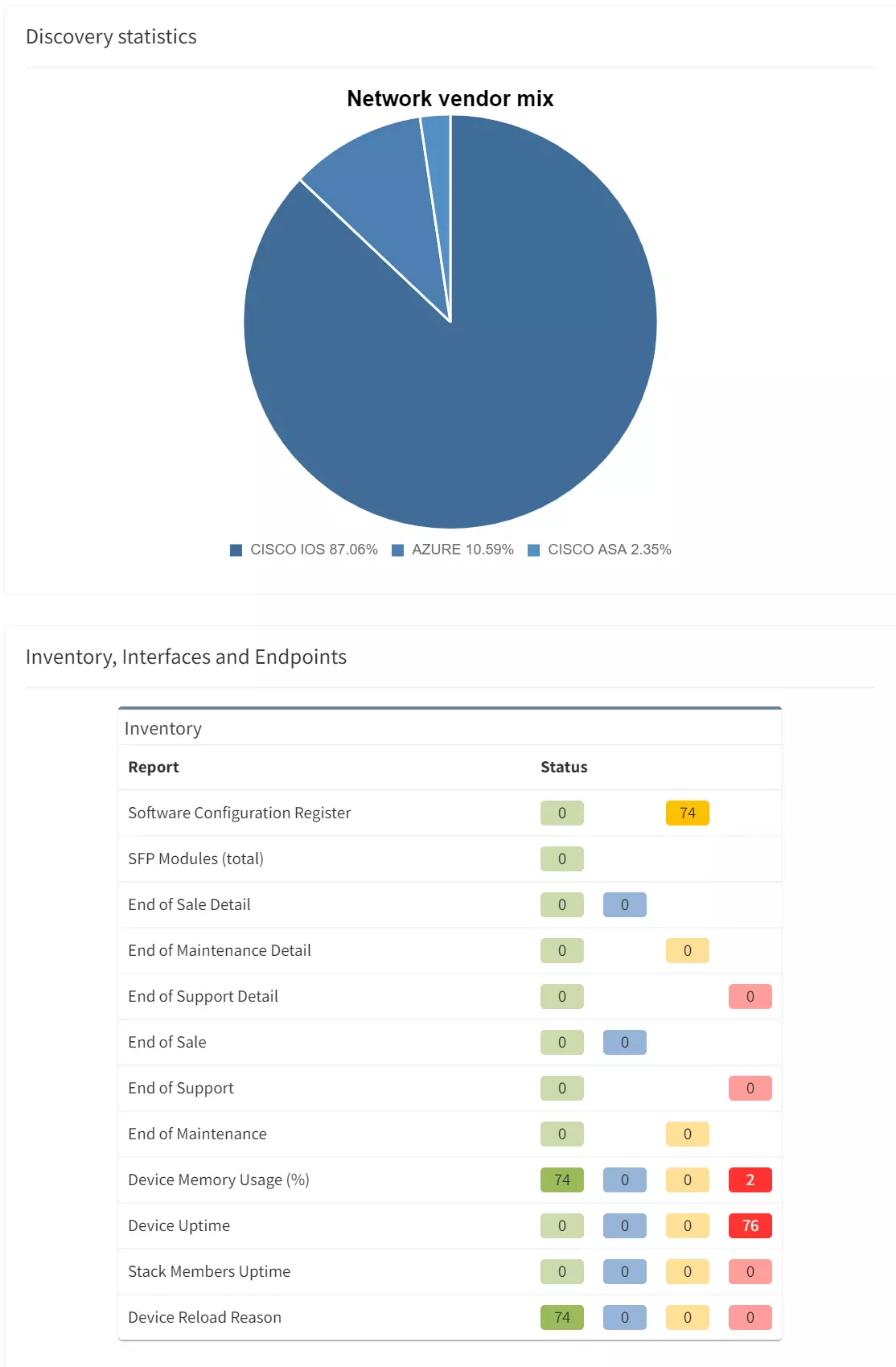
Network assurance can be used to map out your complete network estate by gathering all available device information, including on OSI layers 1 and 2. Network assurance can even gather information on network pieces missing from documentation and add these to network diagrams (e.g.) that Aruba router or core switch you have? Network Assurance solutions like IP Fabric will discover them through CDP/LLDP, routing, and/or ARP information from neighboring devices during discovery.
Because assurance also includes a check on device state, you can see if core switches have missing PSUs, or whether MPLS edge routers are nearing end-of-life.
Network assurance grants you access to network topology diagrams and end-to-end path analysis which does not begin at OSI layer 3. Instead, it grants you the full picture. Furthermore, they give you the ability to build custom intent checks and verify network configuration to provide a more encompassing view of a network.

Well of course it does. Assurance creates a more comprehensive, rounded view of a network estate. All teams can benefit from a well configured NSPM solution, and all of them will find additional benefits from adding network assurance to the mix.
Infrastructure teams: With assurance comes self-updating documentation, more proactive troubleshooting, and rapid detection of issues before an outage occurs. For infrastructure teams, this means a more proactive approach to daily business.
Network security teams: Using assurance, security teams can visualize where rogue devices exist. They are also able to view if, and where, shortcuts in their planned and configured micro-segmentation have been built in, and whether rule changes have been properly implemented. In addition, they can also obtain details on, for example, where AAA needs to be implemented, which switch ports lack NAC configuration, and which (potentially vulnerable) OS versions are running on their firewalls.
Architect teams: Architects can leverage assurance to see where and how new network infrastructure expansions can be realized. With IP Fabric in particular, snapshots can be taken to verify the success of planned changes, both pre- and post-implementation.
Applications teams: App teams can quickly and easily fetch information on available IP addresses and switches/ports. Connectivity can be more proactively verified, and in greater detail.
Without one, the other is limited. In this regard, we should consider network assurance tools like IP Fabric and NSPM tools to be yin and yang. Network assurance is passive, and only reads devices, whereas NSPM is active and can push configuration policies in a standardized manner. Without one, the other is incomplete in a sense.
NSPM can be leveraged by teams to ensure that security policies are applied as they should be across a network. With network assurance in the mix, NSPMs weak points regarding visibility provision are covered through the complete topological overviews and comprehensive state data assurance provides - no matter how fragmented or sprawled.
Even though network assurance can't be a one-stop shop for all of your networking needs, it can complement your existing ecosystem to provide you a fuller picture of your networks interactions and behavior. It covers some of a network engineer's daily tasks in seconds or minutes. Most importantly, it helps improve the overall stability, availability, and security of the networks you manage.
Want to find out more about Network Assurance? Try our free, self-guided demo here to see how you can achieve greater and more contextualized network visibility.
Since the mid-2000s, quite a few network security policy management (NSPM) platforms have arrived on the market. Whilst they are effective at what they do, just how useful are they in isolation? It depends on who you ask. Network security teams would probably agree that NSPM solutions are great, whereas infrastructure teams would likely disagree. But why? What do NSPMs do exactly? And more importantly, is there a way to improve them? We think so. We believe the answer lies in Network Assurance.
NSPM platforms can do quite a bit to improve overall network security:
Based on this list alone, it should be simple enough to put an NSPM solution in place and call it a day, right? After all, my security rules are being checked, and I know what impact data flow is having on my connectivity. Well think again.

While NSPM platforms provide SOME visibility, teams don't necessarily get the full picture that they need. This is because NSPM platforms typically only begin at OSI layer 3, the routing layer. When trying to discover and document your network, NSPMs only provide a restricted view of the entire picture.
Modern networks are inherently fragmented. Combine traditional network elements like routers and switches with a mixture of private and public cloud environments, and suddenly, ensuring comprehensive security policy implementation across all environments becomes more taxing.
Network assurance rounds out this view. As assurance views modern network infrastructures as a 'network-of-networks', it is geared toward understanding how network environments interconnect and interact, and how a change in one area can impact others.
Network assurance can be used to map out your complete network estate by gathering all available device information, including on OSI layers 1 and 2. Network assurance can even gather information on network pieces missing from documentation and add these to network diagrams (e.g.) that Aruba router or core switch you have? Network Assurance solutions like IP Fabric will discover them through CDP/LLDP, routing, and/or ARP information from neighboring devices during discovery.
Because assurance also includes a check on device state, you can see if core switches have missing PSUs, or whether MPLS edge routers are nearing end-of-life.
Network assurance grants you access to network topology diagrams and end-to-end path analysis which does not begin at OSI layer 3. Instead, it grants you the full picture. Furthermore, they give you the ability to build custom intent checks and verify network configuration to provide a more encompassing view of a network.

Well of course it does. Assurance creates a more comprehensive, rounded view of a network estate. All teams can benefit from a well configured NSPM solution, and all of them will find additional benefits from adding network assurance to the mix.
Infrastructure teams: With assurance comes self-updating documentation, more proactive troubleshooting, and rapid detection of issues before an outage occurs. For infrastructure teams, this means a more proactive approach to daily business.
Network security teams: Using assurance, security teams can visualize where rogue devices exist. They are also able to view if, and where, shortcuts in their planned and configured micro-segmentation have been built in, and whether rule changes have been properly implemented. In addition, they can also obtain details on, for example, where AAA needs to be implemented, which switch ports lack NAC configuration, and which (potentially vulnerable) OS versions are running on their firewalls.
Architect teams: Architects can leverage assurance to see where and how new network infrastructure expansions can be realized. With IP Fabric in particular, snapshots can be taken to verify the success of planned changes, both pre- and post-implementation.
Applications teams: App teams can quickly and easily fetch information on available IP addresses and switches/ports. Connectivity can be more proactively verified, and in greater detail.
Without one, the other is limited. In this regard, we should consider network assurance tools like IP Fabric and NSPM tools to be yin and yang. Network assurance is passive, and only reads devices, whereas NSPM is active and can push configuration policies in a standardized manner. Without one, the other is incomplete in a sense.
NSPM can be leveraged by teams to ensure that security policies are applied as they should be across a network. With network assurance in the mix, NSPMs weak points regarding visibility provision are covered through the complete topological overviews and comprehensive state data assurance provides - no matter how fragmented or sprawled.
Even though network assurance can't be a one-stop shop for all of your networking needs, it can complement your existing ecosystem to provide you a fuller picture of your networks interactions and behavior. It covers some of a network engineer's daily tasks in seconds or minutes. Most importantly, it helps improve the overall stability, availability, and security of the networks you manage.
Want to find out more about Network Assurance? Try our free, self-guided demo here to see how you can achieve greater and more contextualized network visibility.