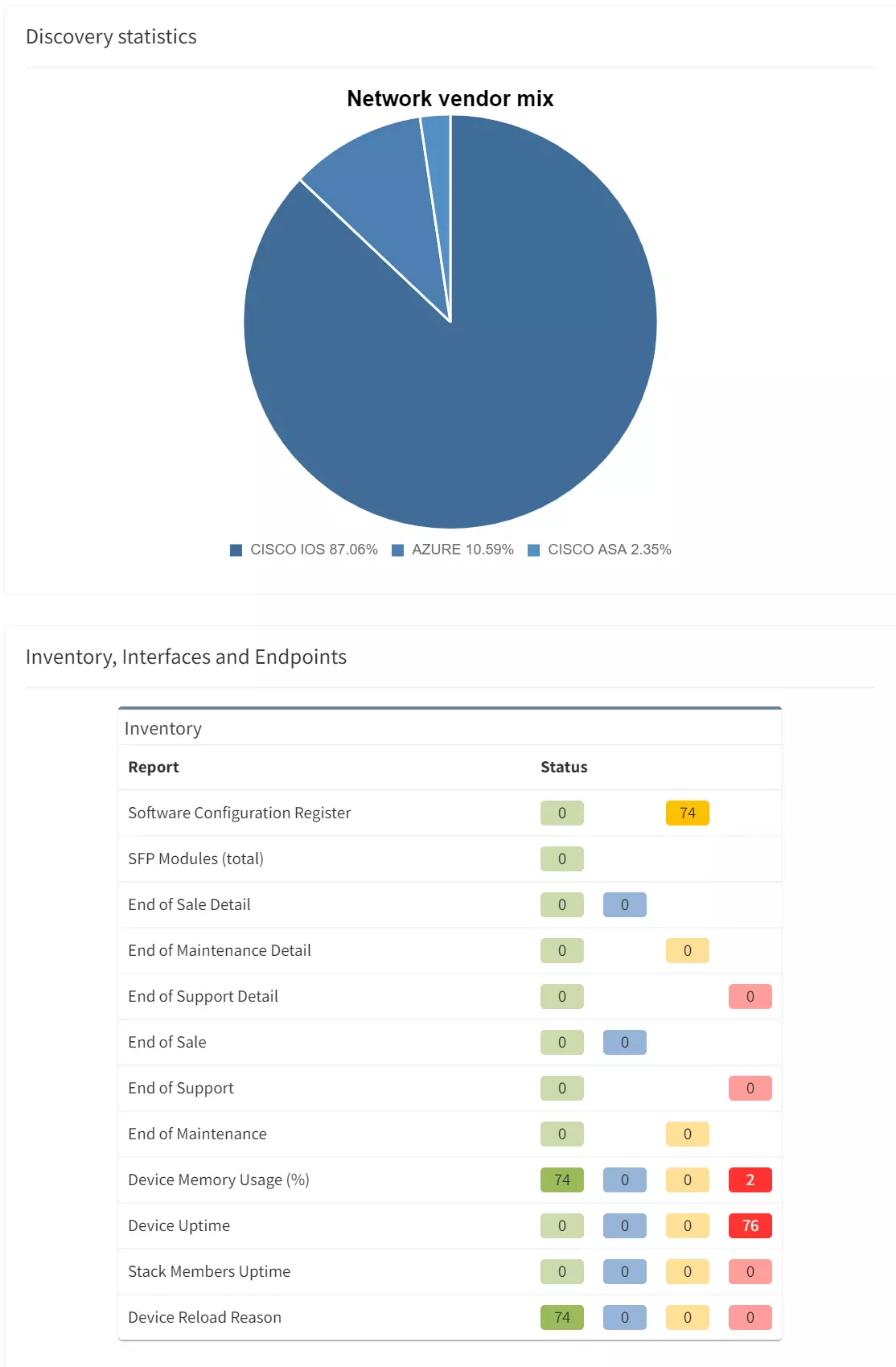
A network security audit is a systematic evaluation of the security of a company’s information systems or network intermediary devices. We evaluate the secureness of the network using a few different sets of criteria, including measuring how well the devices conform to a set of established rules.
A thorough security audit typically assesses the system’s physical configuration, environment, software, information handling processes, and user practices. Traditionally, this process uses up a lot of valuable work hours, and can easily give inaccurate results if a tiny mistake is made anywhere along the way. But today, thanks to IP Fabric, teams can perform this security audit in just under an hour.
Let’s take a look at some of the ways that IP Fabric can help you conduct a network security audit quickly.
When it comes to successfully exporting security policies from SRX, IP Fabric gives you plenty of options.
The very easy one is to export the configuration between security zones to a text file and upload and send them to a customer. But it could be time-consuming for non-Juniper technicians or managers. Also, for some people, it may be difficult to comprehend all the information in the configuration file.
Another option may be buying Junos Space software with the Security Director plugin. Or we could develop any customized script using Junos PyEZ library and export policies to multiple file formats. Both have their downsides.
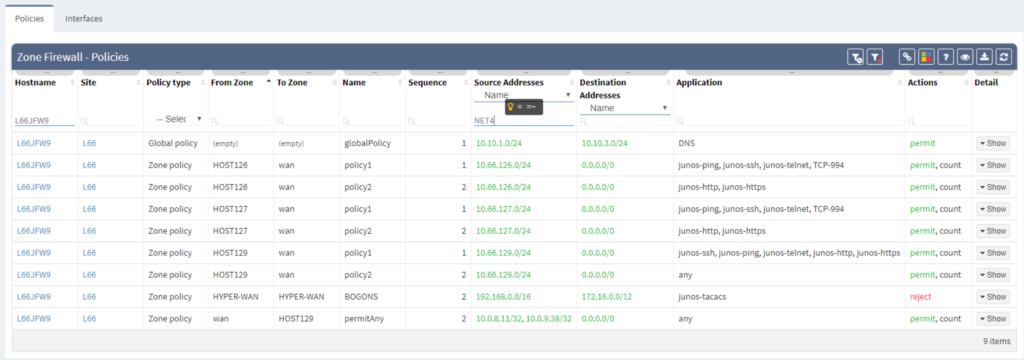
"As a DC service provider, we have implemented a robust firewall cluster that currently supports more than 2000 clients. These clients request the security reports on a daily basis. The reports have to include the most current security policies configuration as well.
As a result of using the IP Fabric platform, we can create and export a comprehensive report anytime. Typically, fulfilling this request would take all day, but with IP Fabric, this entire process takes mere seconds to finish."
In a multivendor environment, enforcing an authentication means verifying that everything is what it claims to be. The purpose of an 802.1x verification is to help you accept or reject users requesting full-access to a network that uses 802.1X protocol.
Today, more and more companies shift towards tighter LAN security. They’re discovering that this process can cost them countless hours on implementation and verification if they try to do it on their own.
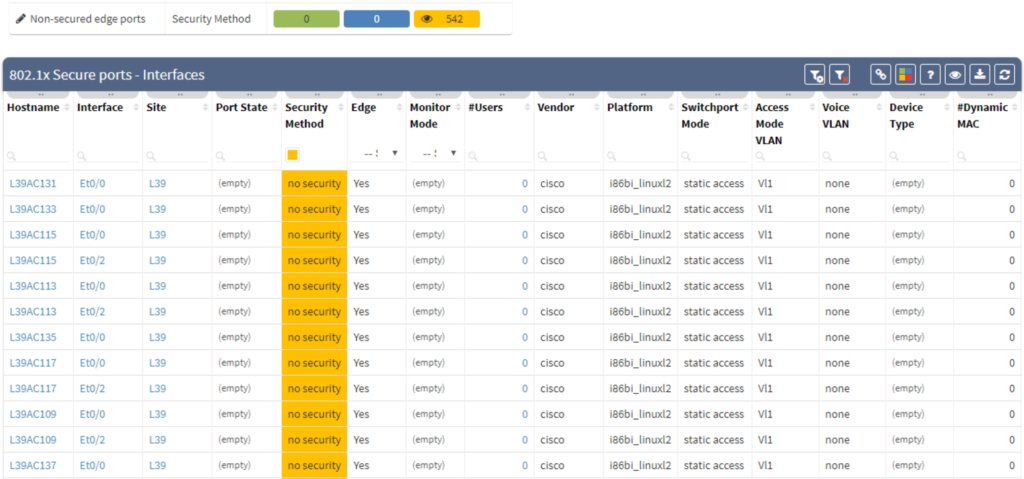
"In our company, we have more than 800 employees at 12 separate locations across the country. Using traditional methods, 802.1X protocol implementation is a long and arduous verification process. It can easily take more than three months to complete.
On the other hand, with the IP Fabric tool, we were able to tackle the verification process almost instantly. The tool simplifies and automates 802.1X verification, allowing us to run it as frequently as needed."
Access-lists (or firewall filters) are a key feature when enhancing security across networks. They deny or grant access to devices based on specific combinations of source, destination IP, destination port, or other kinds of data. ACLs are fast and easy to implement. However, they are difficult to troubleshoot, even when appropriately applied. The IP Fabric platform compiles all of your ACLs into one place, allowing you to compare and correlate rules across all network devices easily.
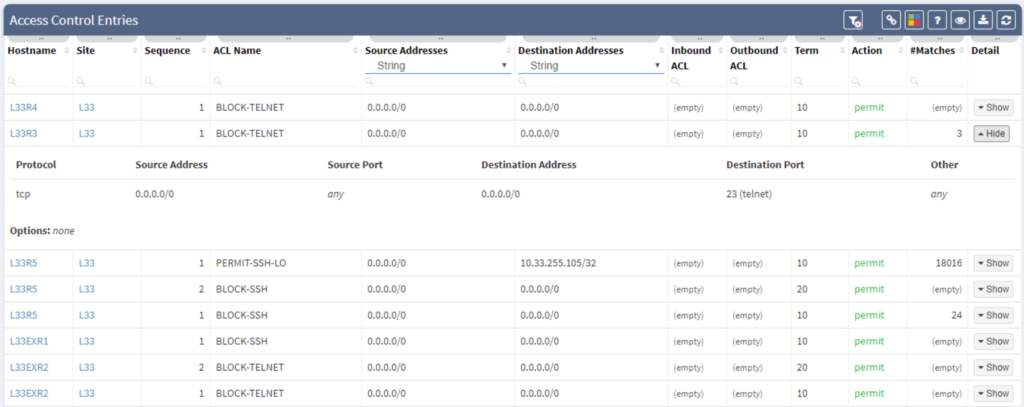
"Our MPLS network has thousands of network devices. To ensure compliance, we need to quickly verify that an up-to-date firewall filter is protecting management loopbacks. The IP Fabric platform can complete this task almost instantly and will give you a comprehensive device list that you can easily export and share."
The Authentication, Authorization, and Accounting system is used to track user activity on an IP-based network and control their access to network resources. It is time-consuming to verify that all network nodes are configured along with the same AAA framework when managing complex network infrastructure.
The IP Fabric platform reduces the amount of time and hassle involved in AAA by giving you a highly detailed overview of all AAA-related information.
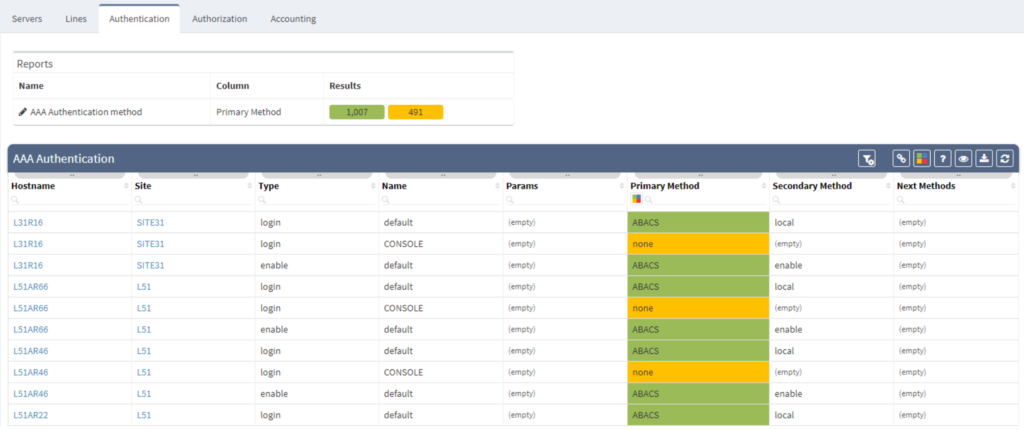
"A few months ago we decided to migrate all of our network devices to a new AAA server, which meant that we also agreed to a change of authorization rules.
The IP Fabric platform made tracking the progress of the migration effortless, meaning we had more time to focus on more critical tasks."
Simple Network Management Protocol (SNMP) and Syslog are the key protocols for maintaining and monitoring network. A network engineer needs to ensure that both protocols are reporting properly to dedicated SNMP and Syslog servers. Above all, one must apply security correctly to this type of communication.
Thanks to IP Fabric, you’ll have a detailed structure report related to these protocols.
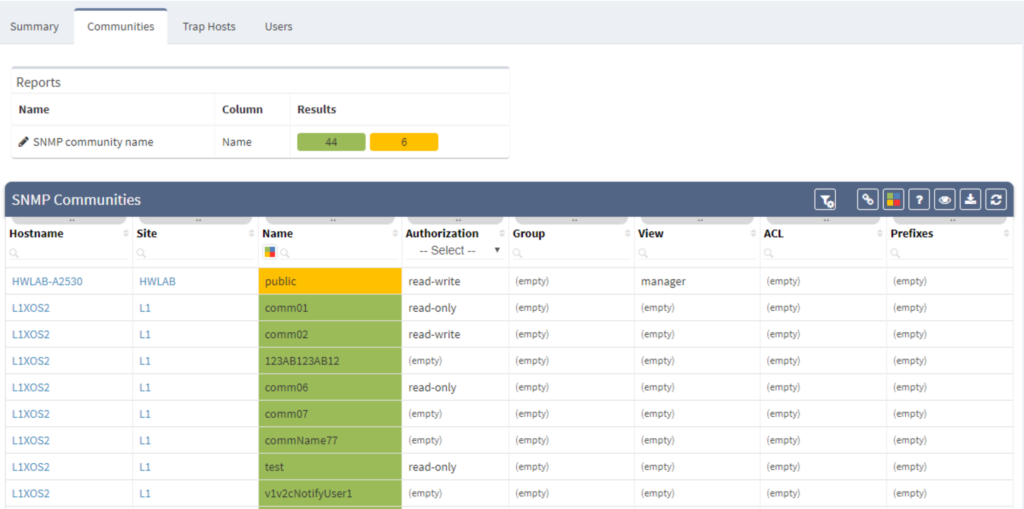
"Over the last 15 years, our network has evolved countless times, and we have lost track of correct SNMP configuration a few times along the way.
Since security is incredibly important to us, we designed the IP Fabric tool to help us verify that all SNMP traffic is sent to dedicated servers and that read-write rules are active at all times."
Interested in learning more about how IP Fabric’s platform can help you with analytics or intended network behavior reporting? Contact us through our website, request a demo, follow this blog, or try our self-guided demo.
A network security audit is a systematic evaluation of the security of a company’s information systems or network intermediary devices. We evaluate the secureness of the network using a few different sets of criteria, including measuring how well the devices conform to a set of established rules.
A thorough security audit typically assesses the system’s physical configuration, environment, software, information handling processes, and user practices. Traditionally, this process uses up a lot of valuable work hours, and can easily give inaccurate results if a tiny mistake is made anywhere along the way. But today, thanks to IP Fabric, teams can perform this security audit in just under an hour.
Let’s take a look at some of the ways that IP Fabric can help you conduct a network security audit quickly.
When it comes to successfully exporting security policies from SRX, IP Fabric gives you plenty of options.
The very easy one is to export the configuration between security zones to a text file and upload and send them to a customer. But it could be time-consuming for non-Juniper technicians or managers. Also, for some people, it may be difficult to comprehend all the information in the configuration file.
Another option may be buying Junos Space software with the Security Director plugin. Or we could develop any customized script using Junos PyEZ library and export policies to multiple file formats. Both have their downsides.
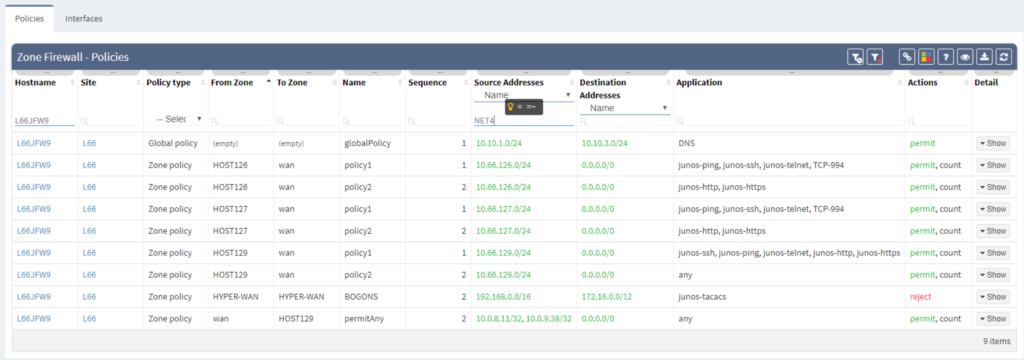
"As a DC service provider, we have implemented a robust firewall cluster that currently supports more than 2000 clients. These clients request the security reports on a daily basis. The reports have to include the most current security policies configuration as well.
As a result of using the IP Fabric platform, we can create and export a comprehensive report anytime. Typically, fulfilling this request would take all day, but with IP Fabric, this entire process takes mere seconds to finish."
In a multivendor environment, enforcing an authentication means verifying that everything is what it claims to be. The purpose of an 802.1x verification is to help you accept or reject users requesting full-access to a network that uses 802.1X protocol.
Today, more and more companies shift towards tighter LAN security. They’re discovering that this process can cost them countless hours on implementation and verification if they try to do it on their own.
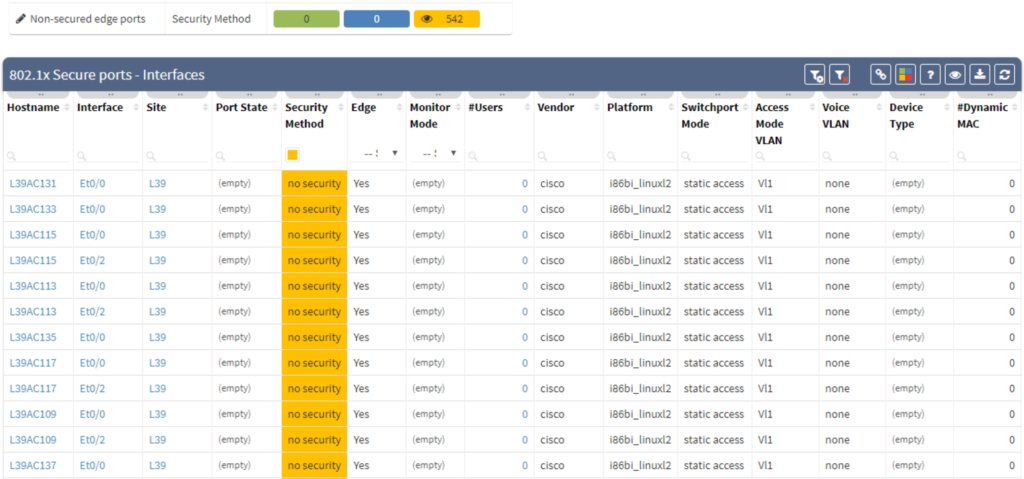
"In our company, we have more than 800 employees at 12 separate locations across the country. Using traditional methods, 802.1X protocol implementation is a long and arduous verification process. It can easily take more than three months to complete.
On the other hand, with the IP Fabric tool, we were able to tackle the verification process almost instantly. The tool simplifies and automates 802.1X verification, allowing us to run it as frequently as needed."
Access-lists (or firewall filters) are a key feature when enhancing security across networks. They deny or grant access to devices based on specific combinations of source, destination IP, destination port, or other kinds of data. ACLs are fast and easy to implement. However, they are difficult to troubleshoot, even when appropriately applied. The IP Fabric platform compiles all of your ACLs into one place, allowing you to compare and correlate rules across all network devices easily.
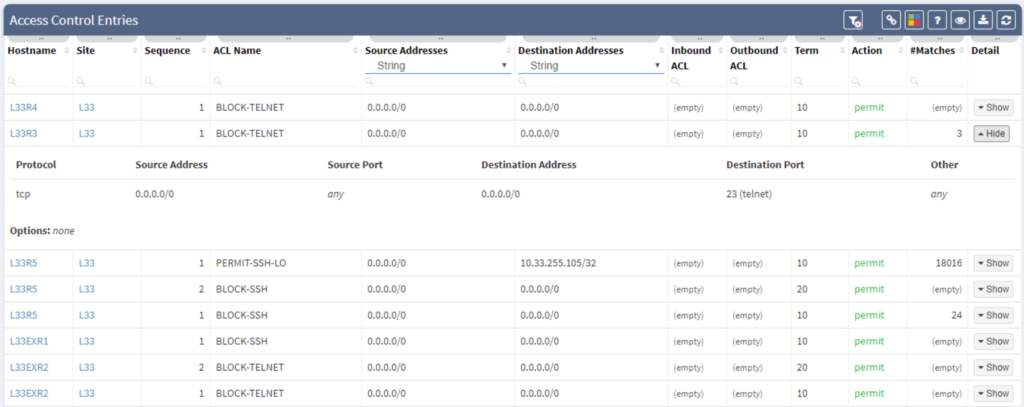
"Our MPLS network has thousands of network devices. To ensure compliance, we need to quickly verify that an up-to-date firewall filter is protecting management loopbacks. The IP Fabric platform can complete this task almost instantly and will give you a comprehensive device list that you can easily export and share."
The Authentication, Authorization, and Accounting system is used to track user activity on an IP-based network and control their access to network resources. It is time-consuming to verify that all network nodes are configured along with the same AAA framework when managing complex network infrastructure.
The IP Fabric platform reduces the amount of time and hassle involved in AAA by giving you a highly detailed overview of all AAA-related information.
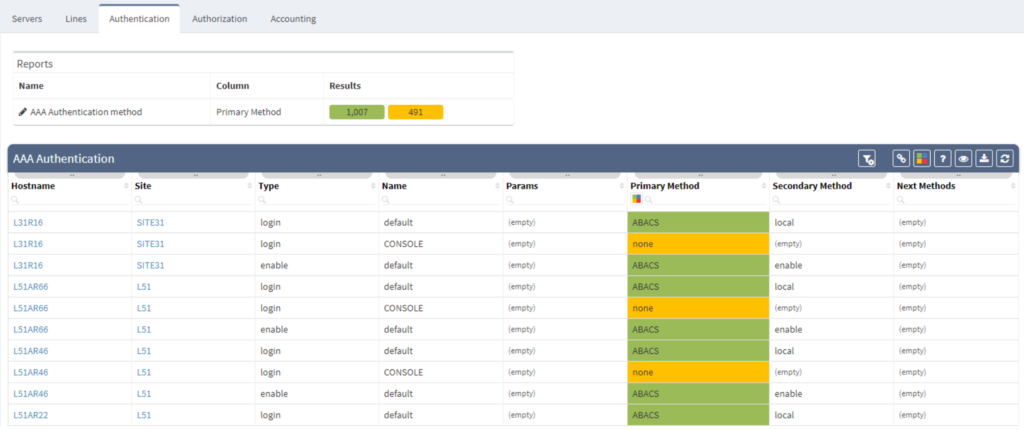
"A few months ago we decided to migrate all of our network devices to a new AAA server, which meant that we also agreed to a change of authorization rules.
The IP Fabric platform made tracking the progress of the migration effortless, meaning we had more time to focus on more critical tasks."
Simple Network Management Protocol (SNMP) and Syslog are the key protocols for maintaining and monitoring network. A network engineer needs to ensure that both protocols are reporting properly to dedicated SNMP and Syslog servers. Above all, one must apply security correctly to this type of communication.
Thanks to IP Fabric, you’ll have a detailed structure report related to these protocols.
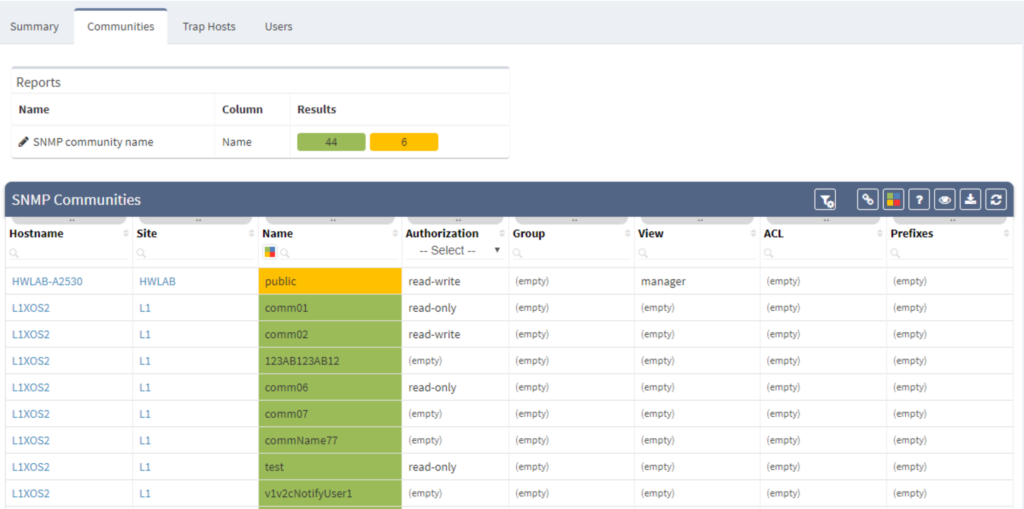
"Over the last 15 years, our network has evolved countless times, and we have lost track of correct SNMP configuration a few times along the way.
Since security is incredibly important to us, we designed the IP Fabric tool to help us verify that all SNMP traffic is sent to dedicated servers and that read-write rules are active at all times."
Interested in learning more about how IP Fabric’s platform can help you with analytics or intended network behavior reporting? Contact us through our website, request a demo, follow this blog, or try our self-guided demo.