In our last post, we discussed the complexity of the operational tooling ecosystem that we use to maintain and support networks. In particular we looked into the following areas:
We discussed the gaps between the existing tools, and hinted that IP Fabric could help improve process and answer questions that traditional tooling cannot. So let's dig a little deeper!
Typically, each vendor of network devices, and each network domain will have variations in the tooling for config management. This can take the form of anything from different libraries to use in scripting languages to complete vendor-specific SDN controllers. These present us with a number of problems, stemming from not being able to ensure that you have a complete vendor neutral view of the whole network. For example,

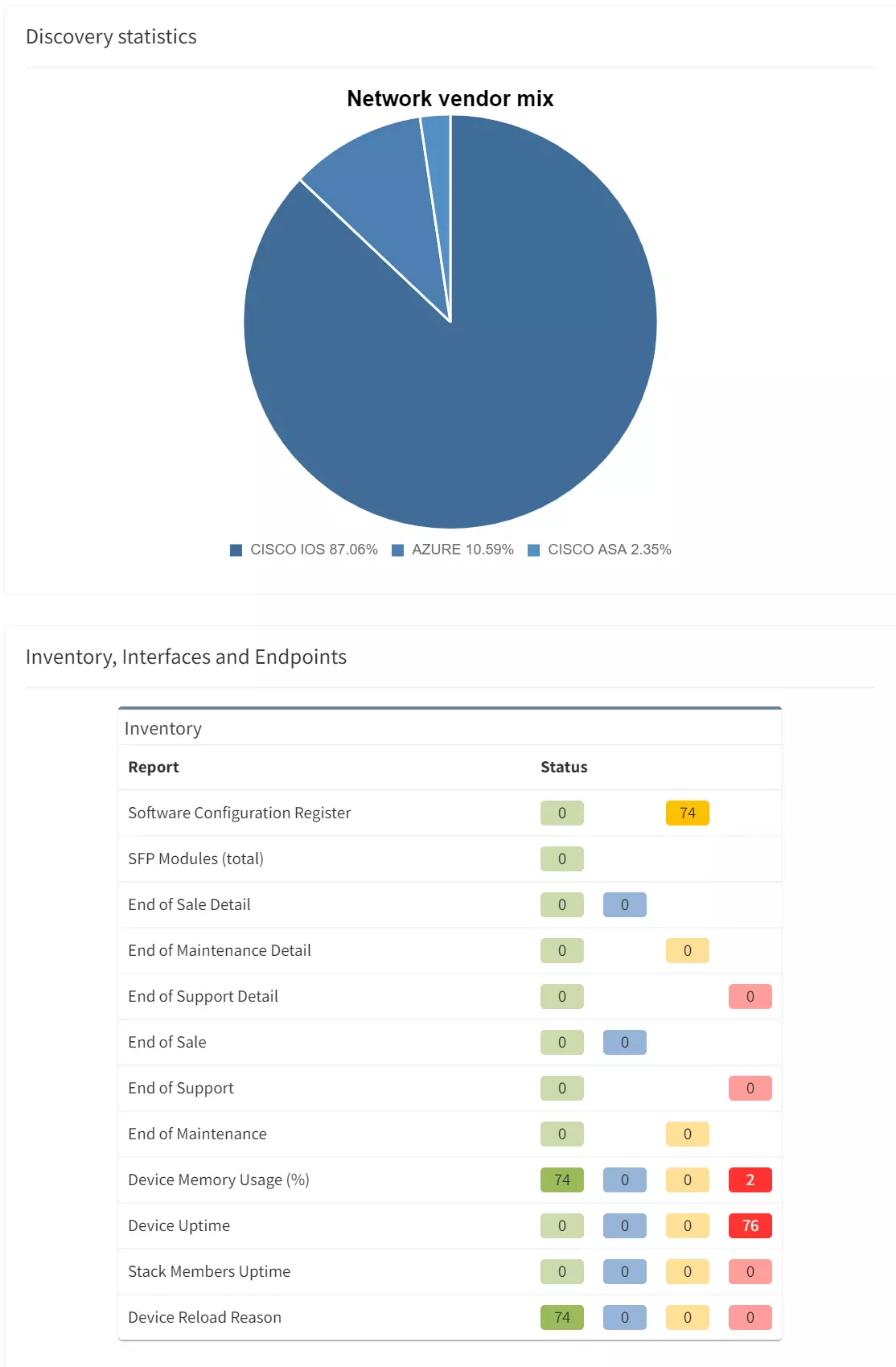
IP Fabric's discovery process allows us to harvest the full operational view of the network, including inventory, configuration and state data. This is then modelled in a vendor neutral form, and its powerful analysis then identifies all the interactions and relationships between devices and nodes. From here, we can deliver intent verification, ensuring the network is behaving as expected, without resorting to crude config file comparison.
The data is retrieved quickly and efficiently and captures a moment in time across the entire network. As such it is possible to compare state from different points in time - such as before and after changes.
As mentioned previously, performance monitoring tooling is focussed either on links, devices or applications. Typically there is no one tool that is able to identify dependencies between the three. Multiple tools may be required due to vendor or platform specifics, and so it is difficult to get an aggregated view.
Also, it is important to ensure those monitoring platforms are kept up to date with changes in the network. As links, devices or applications are added, removed or changed so the monitoring systems should be refreshed, or you are left with holes in your network visibility.

As IP Fabric is regularly refreshing its view of the network it is able to identify changes to inventory and config over time. This data can be used to automatically update monitoring platforms.
IP Fabric's intent verification rules can also be used to validate that - regardless of vendor or platform - devices are configured to allow that monitoring to take place. For example they may need the correct SNMP configuration with an ACL with the appropriate poller addresses.
We can also define other metrics for performance rather than crude measurement of statistics and counters. As the platform has the ability to represent relationships in the network, we can measure stability of peering, or consistency of link parameters for example. Such measurements can proactively indicate where performance issues may occur in the future.
In a similar vein, to get the most out of event management systems, it is necessary to ensure that all devices in the network are configured appropriately to send logging and event information to the correct servers. Verification rules are simple to build in IP Fabric to ensure this intent is met.

Inventory and topology data can also be passed from IP Fabric to a central correlation engine over API. This can be used to ensure that the relationships between devices are understood for root cause analysis or SIEM purposes.
IP Fabric can also contribute as a correlation data source, providing its unique additional performance measures as a proactive indication that an event may occur at some point in the future.
In order to ensure that the network is supportable and manageable, documentation has to be kept accurate and up to date. This is the bane of the Network Engineer's life as every single change, and every single issue should be represented in updates to whichever static documents are kept. Significant amounts of time and effort are put into this activity: even so, it is rarely completed.
Good documentation is key for the troubleshooting elements of incident and problem management. It can also be seen to be essential for preparation and planning for implementation and testing of changes. And updating it should be a mandatory post-change activity.

IP Fabric's discovered view of the network serves as fully updated centralised end-to-end documentation. It stores a wealth of data about inventory, configuration and state in tables which are accessible through Web UI and API. And it also provides powerful multi-layered visualisation of the network sites themselves, and the end-to-end paths through the network that application traffic takes.
Complete or partial snapshots can be taken as part of the change delivery process. They would be used with intent verification rules and end-to-end path checks to ensure that changes have been executed correctly and have had the desired outcome.
The CMDB presents data about the network (and often other IT infrastructure) to other areas of the business which can then be used for non-operational purposes. Typical uses might include managing support contracts, licence subscriptions, circuit rentals or planning refresh programmes.
Thus it is imperative that this is an accurate reflection of the operating network and that the CMDB reflects the inventory that lives in the operational systems.

IP Fabric's discovered inventory can be used to maintain and update the CMDB inventory in the simplest terms. Devices are allocated to sites during the discovery process so it is possible to maintain the location of devices and the modules, power supplies and optics that sit inside them.
IP Fabric also tracks the end-of-life status of network elements and thus can identify lists of devices that need to be replaced if maintenance or support status is required to be upheld.
It's clear that IP Fabric can be used to fill the gaps between all your operational tooling. Use it as the foundation - the source of observed truth in your network. Update other platforms with its discovered inventory data as a first step. Then consider using intent verification for compliance and change validation ... the possibilities are endless!
If you have found this article helpful, please follow our company’s LinkedIn or Blog, where more content will be emerging. If you would like to test our solution to see for yourself how IP Fabric can help you manage your network more effectively, please contact us through www.ipfabric.io.
In our last post, we discussed the complexity of the operational tooling ecosystem that we use to maintain and support networks. In particular we looked into the following areas:
We discussed the gaps between the existing tools, and hinted that IP Fabric could help improve process and answer questions that traditional tooling cannot. So let's dig a little deeper!
Typically, each vendor of network devices, and each network domain will have variations in the tooling for config management. This can take the form of anything from different libraries to use in scripting languages to complete vendor-specific SDN controllers. These present us with a number of problems, stemming from not being able to ensure that you have a complete vendor neutral view of the whole network. For example,

IP Fabric's discovery process allows us to harvest the full operational view of the network, including inventory, configuration and state data. This is then modelled in a vendor neutral form, and its powerful analysis then identifies all the interactions and relationships between devices and nodes. From here, we can deliver intent verification, ensuring the network is behaving as expected, without resorting to crude config file comparison.
The data is retrieved quickly and efficiently and captures a moment in time across the entire network. As such it is possible to compare state from different points in time - such as before and after changes.
As mentioned previously, performance monitoring tooling is focussed either on links, devices or applications. Typically there is no one tool that is able to identify dependencies between the three. Multiple tools may be required due to vendor or platform specifics, and so it is difficult to get an aggregated view.
Also, it is important to ensure those monitoring platforms are kept up to date with changes in the network. As links, devices or applications are added, removed or changed so the monitoring systems should be refreshed, or you are left with holes in your network visibility.

As IP Fabric is regularly refreshing its view of the network it is able to identify changes to inventory and config over time. This data can be used to automatically update monitoring platforms.
IP Fabric's intent verification rules can also be used to validate that - regardless of vendor or platform - devices are configured to allow that monitoring to take place. For example they may need the correct SNMP configuration with an ACL with the appropriate poller addresses.
We can also define other metrics for performance rather than crude measurement of statistics and counters. As the platform has the ability to represent relationships in the network, we can measure stability of peering, or consistency of link parameters for example. Such measurements can proactively indicate where performance issues may occur in the future.
In a similar vein, to get the most out of event management systems, it is necessary to ensure that all devices in the network are configured appropriately to send logging and event information to the correct servers. Verification rules are simple to build in IP Fabric to ensure this intent is met.

Inventory and topology data can also be passed from IP Fabric to a central correlation engine over API. This can be used to ensure that the relationships between devices are understood for root cause analysis or SIEM purposes.
IP Fabric can also contribute as a correlation data source, providing its unique additional performance measures as a proactive indication that an event may occur at some point in the future.
In order to ensure that the network is supportable and manageable, documentation has to be kept accurate and up to date. This is the bane of the Network Engineer's life as every single change, and every single issue should be represented in updates to whichever static documents are kept. Significant amounts of time and effort are put into this activity: even so, it is rarely completed.
Good documentation is key for the troubleshooting elements of incident and problem management. It can also be seen to be essential for preparation and planning for implementation and testing of changes. And updating it should be a mandatory post-change activity.

IP Fabric's discovered view of the network serves as fully updated centralised end-to-end documentation. It stores a wealth of data about inventory, configuration and state in tables which are accessible through Web UI and API. And it also provides powerful multi-layered visualisation of the network sites themselves, and the end-to-end paths through the network that application traffic takes.
Complete or partial snapshots can be taken as part of the change delivery process. They would be used with intent verification rules and end-to-end path checks to ensure that changes have been executed correctly and have had the desired outcome.
The CMDB presents data about the network (and often other IT infrastructure) to other areas of the business which can then be used for non-operational purposes. Typical uses might include managing support contracts, licence subscriptions, circuit rentals or planning refresh programmes.
Thus it is imperative that this is an accurate reflection of the operating network and that the CMDB reflects the inventory that lives in the operational systems.

IP Fabric's discovered inventory can be used to maintain and update the CMDB inventory in the simplest terms. Devices are allocated to sites during the discovery process so it is possible to maintain the location of devices and the modules, power supplies and optics that sit inside them.
IP Fabric also tracks the end-of-life status of network elements and thus can identify lists of devices that need to be replaced if maintenance or support status is required to be upheld.
It's clear that IP Fabric can be used to fill the gaps between all your operational tooling. Use it as the foundation - the source of observed truth in your network. Update other platforms with its discovered inventory data as a first step. Then consider using intent verification for compliance and change validation ... the possibilities are endless!
If you have found this article helpful, please follow our company’s LinkedIn or Blog, where more content will be emerging. If you would like to test our solution to see for yourself how IP Fabric can help you manage your network more effectively, please contact us through www.ipfabric.io.