For the record, it's not enough anymore to add a firewall to your network to claim it is secure. Networking is more pervasive than ever. More devices are connected each day. And networks have become the foundation for more services and processes than we ever dreamed of. With this shift, the attack exposure surface has increased and we recognise a need for change. We need to protect our systems from threats wherever they might come from, not just the "outside". "Trusted" endpoints are given privileged access to the infrastructure: we have to accept that they may be compromised. And so we need to harden the infrastructure to defend against a privileged attacker.
So, while a perimeter security appliance is always a good thing, other elements such as authenticated network access, segmentation, and secured infrastructure become as important as a strong traffic security policy.
A key element to this is ensuring the devices that make up the network are not vulnerable to attack. The US government-sponsored Mitre Corporation run the Common Vulnerability and Exposure (CVE) programme. The purpose of this programme is to identify, define, and catalog publicly disclosed vulnerabilities in software and infrastructure. An identifier is assigned to each vulnerability, then it is classified and assessed and added to the central repository, hosted by NIST. Organisations can then use the data in the repository to assess their exposure.
Typically, vendors make this data available to their support customers in order to assist with their lifecycle management. Up until fairly recently, NIST provided access to the National Vulnerability Database (NVD) to anyone who wanted it in the form of a feed file. As of June 2020, the preferred method is to make a REST API request, which opens up a whole host of opportunities! Just one API call can give you the list of the CVEs that relate to a particular model in a family of vendor's equipment running a particular code version ...
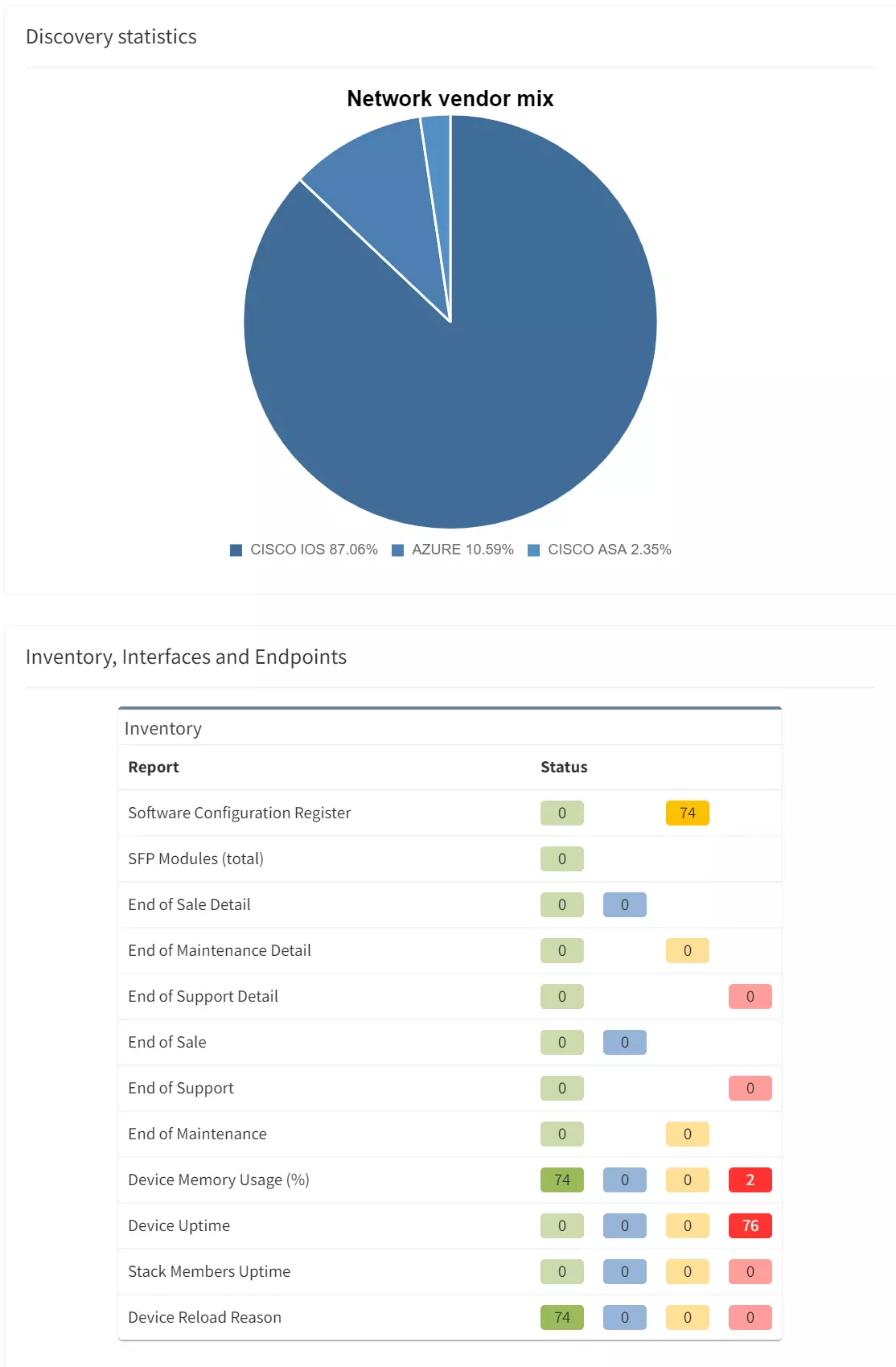
IP Fabric's market-leading discovery maps out your network hop-by-hop in an automated fashion, regularly, in scheduled snapshots. Each snapshot contains a complete model of your network at the point in time, including of course, device inventory, code version and so on.
Combine that data with the CVE database, and you have all the data you could need to discover just which CVEs could affect your network infrastructure!
You could take that a step further of course. IP Fabric's model also tracks the configuration deployed to devices, the network topology and the hosts that are connected to a particular device at a point in time. Using the metadata from the model then, once you have identified the CVEs affecting devices in your environment, you could:
Using IP Fabric's extensive REST API, the data in the model we describe above is easily extracted from the platform. The API call to fetch that data is simple enough. Create an API token, then issue a POST request to the API endpoint 'tables/inventory/devices' on your IP Fabric server, to fetch the inventory from the required snapshot, eg:
curl "https://demoX.wordpress-625423-2416527.cloudwaysapps.com/api/v1/tables/inventory/devices" -X POST -H "X-API-Token: XXXXXXXXXXXX" -d '{"columns":["hostname","vendor","family","version"],"snapshot":"$last"}'
From that output, you can then loop through the list of devices returned and assemble a request to search the NIST database, eg:
curl "http://services.nvd.nist.gov/rest/json/cves/1.0?cpeMatchString=cpe:2.3:*:<vendor>:<family>:<version>"
This returns a JSON data structure containing the list of CVEs that apply to the device in question. For each CVE item, you have a description of the CVE, the source of the report, a classification of the threat level in terms of impact and exploitability and so on. Use a cript to make that API call, and you can then continue your own processing of the list to cross-check the impact of those CVEs with the role and status of the devices in IP Fabric's model.
In IP Fabric's #CommunityFabric github repo, there is an example script that makes these calls into IP Fabric and the NIST database for you. It uses a very simple API Client which keeps the code readable and easy to modify. You'll shortly find a video on our Youtube channel (https://youtube.com/c/ipfabric) which shows just how to use the script in more detail.
For the record, it's not enough anymore to add a firewall to your network to claim it is secure. Networking is more pervasive than ever. More devices are connected each day. And networks have become the foundation for more services and processes than we ever dreamed of. With this shift, the attack exposure surface has increased and we recognise a need for change. We need to protect our systems from threats wherever they might come from, not just the "outside". "Trusted" endpoints are given privileged access to the infrastructure: we have to accept that they may be compromised. And so we need to harden the infrastructure to defend against a privileged attacker.
So, while a perimeter security appliance is always a good thing, other elements such as authenticated network access, segmentation, and secured infrastructure become as important as a strong traffic security policy.
A key element to this is ensuring the devices that make up the network are not vulnerable to attack. The US government-sponsored Mitre Corporation run the Common Vulnerability and Exposure (CVE) programme. The purpose of this programme is to identify, define, and catalog publicly disclosed vulnerabilities in software and infrastructure. An identifier is assigned to each vulnerability, then it is classified and assessed and added to the central repository, hosted by NIST. Organisations can then use the data in the repository to assess their exposure.
Typically, vendors make this data available to their support customers in order to assist with their lifecycle management. Up until fairly recently, NIST provided access to the National Vulnerability Database (NVD) to anyone who wanted it in the form of a feed file. As of June 2020, the preferred method is to make a REST API request, which opens up a whole host of opportunities! Just one API call can give you the list of the CVEs that relate to a particular model in a family of vendor's equipment running a particular code version ...
IP Fabric's market-leading discovery maps out your network hop-by-hop in an automated fashion, regularly, in scheduled snapshots. Each snapshot contains a complete model of your network at the point in time, including of course, device inventory, code version and so on.
Combine that data with the CVE database, and you have all the data you could need to discover just which CVEs could affect your network infrastructure!
You could take that a step further of course. IP Fabric's model also tracks the configuration deployed to devices, the network topology and the hosts that are connected to a particular device at a point in time. Using the metadata from the model then, once you have identified the CVEs affecting devices in your environment, you could:
Using IP Fabric's extensive REST API, the data in the model we describe above is easily extracted from the platform. The API call to fetch that data is simple enough. Create an API token, then issue a POST request to the API endpoint 'tables/inventory/devices' on your IP Fabric server, to fetch the inventory from the required snapshot, eg:
curl "https://demoX.wordpress-625423-2416527.cloudwaysapps.com/api/v1/tables/inventory/devices" -X POST -H "X-API-Token: XXXXXXXXXXXX" -d '{"columns":["hostname","vendor","family","version"],"snapshot":"$last"}'
From that output, you can then loop through the list of devices returned and assemble a request to search the NIST database, eg:
curl "http://services.nvd.nist.gov/rest/json/cves/1.0?cpeMatchString=cpe:2.3:*:<vendor>:<family>:<version>"
This returns a JSON data structure containing the list of CVEs that apply to the device in question. For each CVE item, you have a description of the CVE, the source of the report, a classification of the threat level in terms of impact and exploitability and so on. Use a cript to make that API call, and you can then continue your own processing of the list to cross-check the impact of those CVEs with the role and status of the devices in IP Fabric's model.
In IP Fabric's #CommunityFabric github repo, there is an example script that makes these calls into IP Fabric and the NIST database for you. It uses a very simple API Client which keeps the code readable and easy to modify. You'll shortly find a video on our Youtube channel (https://youtube.com/c/ipfabric) which shows just how to use the script in more detail.